The earlier pardus was based on gentoo, it wasnt an entirely built distro but more orginal than a debian with some make up. But gentoo was more flexible than a 'readily packaged' debian.
In my opinion debian (and its offsprings) is widely used, and it could be easier to develop apps or port apps developed for debian based distros (specially like ubuntu , it is most common desktop distro which many companies develop apps for them like spotify, and now there are something called sandboxing and containerizing and things became more fun).
Besides that, debian is 'free' same as 'gentoo' it is a preference to built a distro on whichever suits best for the purpose. It isnt like debian has something which is not free or it is worse than gentoo.
What is bad, besides all, the efforts made for earlier pardus could have been made for the newer version and we could have a better distro which can be widely used in public services, at ministiries, army, universities and so on. Sadly, despite of earlier pardus made up with dire efforts of ambitious individuals, and people have spent their time to build something good, some sneaky people has realized they can rip off more money just by putting some make up on debian. And this has ended pardus figuratively, and turned it into a debian with some make up with quite a few efforts being put into. It isnt about being gentoo or debian but whole mindset has changed regarding to the project.
Personally, i still wouldnt use it because i havent got used to be on debian or gentoo based systems. I use CentOS on servers and desktop, fedora at my laptop.
To really be capable of hardening your military industry and defense equipment against the danger of cyber attacks or cyber surveillane, a whole ecosystem of products has to be created.
1. At the top you need to develop the control software for your armament and the applications used for design and development by the industry (e.g. Simulation Tools, CAD tools, etc). If you use foreign tools, these are very likely to contain hidden code that provides an interested actor highly confidential data about your products.
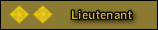
2. Underneath this, you need domestically developed operating systems. Windows and Linux won't cut it here because you cannot trust them. You will need to develop a bunch of home-grown OSes suitable for real-time and security-critical applications, or adopt something already already developed in this space. These products are built with security as the primary design goal.
Although for commercial use it is okay to develop a Linux distro or they could switch to something like ReactOS which is an open source Windows clone! It can even run existing Windows applications, and the project is by the looks of it quite desperate for funding and manpower. Not as much of a mess as linux is but either way neither Linux nor Windows/ReactOS are really suitable for defense products because you don't have control over the whole codebase.
3. Next you will need domestically developed compilers and libraries whose code you control and can audit and patch with full authority. You cannot really trust the code if you can't trust the compiler or the libraries you use.
4. Underneath this you will need to develop the hardware like CPUs, FPGAs, DSPs, RAM, flash storage and basically all the components that can contain hardware backdoors. Domestic processors are especially critical here because of how much they can affect the performance of your products, and also because a backdoor in them can negate every other security measure you have taken elsewhere.
5. Finally, you will need to develop your own semiconductor manufacturing equipment. If the fabrication equipment comes from overseas, you can never trust the circuitry it prints. This is also a highly profitable and niche industry.
Of course, all this requires such a broad effort that it will be impossible to develop the entire ecosystem at a single organization or in a centralized manner. The entire private sector IT/Electronics industry will have to be mobilized and incentivized for this and most of the work will be done by universities and small private sector enterprises. But you cannot ignore any single one of these areas, because if you don't have a domestic solution available, you are still vulnerable to an embargo and you won't be able to defend against your enemies in the cyberspace.