Bratva
PDF THINK TANK: ANALYST

- Joined
- Jun 8, 2010
- Messages
- 13,827
- Reaction score
- 67
- Country
- Location
Putting a kill switch on a major weapon system is akin to signing your own death warrant or bankruptcy as a defense manufacturer. Nobody will EVER buy from that company again.
As such this fiction needs to be kept in the fiction section. What suppliers can possibly do is to provide specifications/frequencies and encryption algorithms of systems provided to the end users to a third party under political pressure. In that case too, it does not render the systems useless.
An example of this is what the French did for the British with regards to the Exocet system during the Falklands war.
It is no longer a fiction. America do implant "beacons" in its equipment. No It didnt kill the reputation of the company back then and it is still a fortune 500 company. Because people and governments dont care that America is implanting chips in to the hardware being shipped to them.
Photos of an NSA “upgrade” factory show Cisco router getting implant
Servers, routers get “beacons” implanted at secret locations by NSA’s TAO team.
SEAN GALLAGHER - 5/14/2014, 10:30 PM
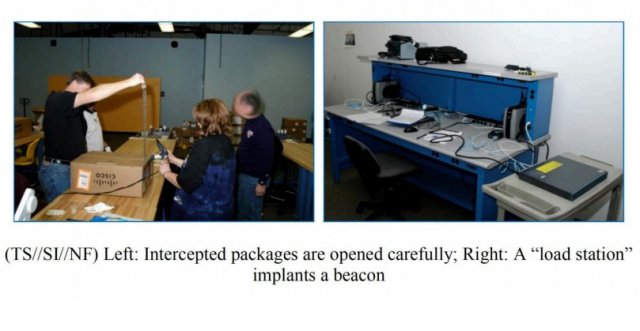
NSA techs perform an unauthorized field upgrade to Cisco hardware in these 2010 photos from an NSA document.
259WITH 170 POSTERS PARTICIPATING
FURTHER READING
NSA hacker in residence dishes on how to “hunt” system admins
A document included in the trove of National Security Agency files released with Glenn Greenwald’s book No Place to Hide details how the agency’s Tailored Access Operations (TAO) unit and other NSA employees intercept servers, routers, and other network gear being shipped to organizations targeted for surveillance and install covert implant firmware onto them before they’re delivered.
These Trojan horse systems were described by an NSA manager as being “some of the most productive operations in TAO because they pre-position access points into hard target networks around the world.”
The document, a June 2010 internal newsletter article by the chief of the NSA’s Access and Target Development department (S3261) includes photos (above) of NSA employees opening the shipping box for a Cisco router and installing beacon firmware with a “load station” designed specifically for the task.
The NSA manager described the process:
Here’s how it works: shipments of computer network devices (servers, routers, etc,) being delivered to our targets throughout the world are intercepted. Next, they are redirected to a secret location where Tailored Access Operations/Access Operations (AO-S326) employees, with the support of the Remote Operations Center (S321), enable the installation of beacon implants directly into our targets’ electronic devices. These devices are then re-packaged and placed back into transit to the original destination. All of this happens with the support of Intelligence Community partners and the technical wizards in TAO.
https://arstechnica.com/tech-policy...show-cisco-router-getting-implant/?comments=1
How the NSA snooped on encrypted Internet traffic for a decade
Exploit against Cisco's PIX line of firewalls remotely extracted crypto keys.
DAN GOODIN - 8/19/2016, 11:11 PM

Enlarge
NSA
120WITH 70 POSTERS PARTICIPATING, INCLUDING STORY AUTHOR
In a revelation that shows how the National Security Agency was able to systematically spy on many Cisco Systems customers for the better part of a decade, researchers have uncovered an attack that remotely extracts decryption keys from the company's now-decommissioned line of PIX firewalls.
The discovery is significant because the attack code, dubbed BenignCertain, worked on PIX versions Cisco released in 2002 and supported through 2009. Even after Cisco stopped providing PIX bug fixes in July 2009, the company continued offering limited service and support for the product for an additional four years. Unless PIX customers took special precautions, virtually all of them were vulnerable to attacks that surreptitiously eavesdropped on their VPN traffic. Beyond allowing attackers to snoop on encrypted VPN traffic, the key extraction also makes it possible to gain full access to a vulnerable network by posing as a remote user.
BenignCertain's capabilities were tentatively revealed in this blog post from Thursday, and they were later confirmed to work on real-world PIX installations by three separate researchers. Before the confirmation came, Ars asked Cisco to investigate the exploit. The company declined, citing this policy for so-called end-of-life products. The exploit helps explain documents leaked by NSA contractor Edward Snowden and cited in a 2014 article that appeared in Der Spiegel. The article reported that the NSA had the ability to decrypt more than 1,000 VPN connections per hour.
"It shows that the NSA had the ability to remotely extract confidential keys from Cisco VPNs for over a decade," Mustafa Al-Bassam, a security researcher at payments processing firm Secure Trading, told Ars. "This explains how they were able to decrypt thousands of VPN connections per minute as shown in documents previously published by Der Spiegel."
The revelation is also concerning because data returned by the Shodan search engine indicate more than 15,000 networks around the world still use PIX, with the Russian Federation, the US, and Australia being the top three countries affected. Last weekend's release of BenignCertain and dozens of other NSA-connected attack tools means even relatively low-skilled hackers can now carry out the same advanced attack. Analysis of the exploit binary shows BenignCertain targeted PIX versions 5.3(9) through 6.3(4). The researchers, however, were able to make the key-extraction technique work against version 6.3(5) as well.
https://arstechnica.com/information...-exploit-shows-how-nsa-decrypted-vpn-traffic/
This is just the tip of iceberg how Americans exploited their own products to spy on allies and adversaries alike. Do you know the Whatever American Network/IT gear that is shipped comes with a warning? that cryptography in the device is intentionally weak than what is used in America? Because As per american laws , exporting stronger cryptographic devices is prohibited.
So defense systems can have Beacons installed in it which sends data back to its Master source. Not a kill switch but a device to keep tabs on someone
Link-16, MIDS, Sniper and EW pods of PAF F-16 requires encryption keys to work. And these keys are provided to Pakistan by USA. So IF USA dont provide the encryption keys, the equipment will not work as intended and if they the provide the keys it means they got an upper hand in knowing what you are doing. So Yes, American firms doesnt care about such things because they know No one will stop from buying them and this is true!
USA last year Reprimanded Pakistan for Transferring Block-52 to Unauthorized Bases and FOB's It was a wartime scenario hence they let it slide and didnt needle Pakistan much
State Department Reprimanded Pakistan for Misusing F-16s, Document Shows
A source who viewed the August letter, written by Andrea Thompson, then-undersecretary of State for Arms Control and International Security Affairs,
Addressed to the head of the Pakistani air force, Air Chief Marshal Mujahid Anwar Khan, the letter began by relaying the State Department's confirmation that Pakistan had moved the F-16s and accompanying American-made missiles to unapproved forward operating bases in defiance of its agreement with the U.S. Using diplomatic language, Thompson, who has since left government, warned the Pakistanis that their behavior risked allowing these weapons to fall into the hands of malign actors and "could undermine our shared security platforms and infrastructures."
Thompson, a career military intelligence officer who first entered the administration as Vice President Mike Pence's national security adviser, admonished Pakistan in the letter for having "relocated, maintained and operated" the American made F-16s and the AMRAAM missiles they use from forward operating bases not approved under the original terms of the sale. The former Army colonel, who left the White House in September, also expressed concern at the access Pakistani officials allowed American weapons inspectors.
The History Behind Kashmir
"While we understand from you that these aircraft movements were done in support of national defense objectives," Thompson wrote in the letter, "the U.S. government considers the relocation of aircraft to non-U.S. government authorized bases concerning and inconsistent with the F-16 Letter of Offer and Acceptance."
"Such actions could subject sensitive U.S.-technologies to diversion to or access by third parties, and could undermine our shared security platforms and infrastructures," Thompson wrote.
In her letter, Thompson raised concerns about American access to the bases and the U.S.-made equipment there. She said it had been four years since Office of Defense Representative–Pakistan – the office that carries out defense cooperation with partner countries – had been allowed to perform an assessment of the security vulnerabilities on the Pakistani bases
https://www.usnews.com/news/world-r...n-in-august-for-misusing-f-16s-document-shows
So If we are seeing a fully loaded Block-52 in Kamra, it simply means that Kamra is on the approved and authorized list of Airbases that it can visit peacetime. And doesnt let Americans moans once again that Pakistan is violating the agreement by not reporting f-16 movement.








